This plan outlines and further breaks down the necessary steps for implementing East Tennessee State University’s Information Security Strategic Plan over the next five years. It identifies the minimum set of required high level steps needed to accomplish each strategic goal. It attempts to identify university stakeholders associated with each high-level unit of effort. Finally, it provides strategic goals’ dependencies which may affect the overall implementation timeline. Contrary to the Information Security Strategic plan, this is a dynamic plan, and is likely to require periodic reviews.
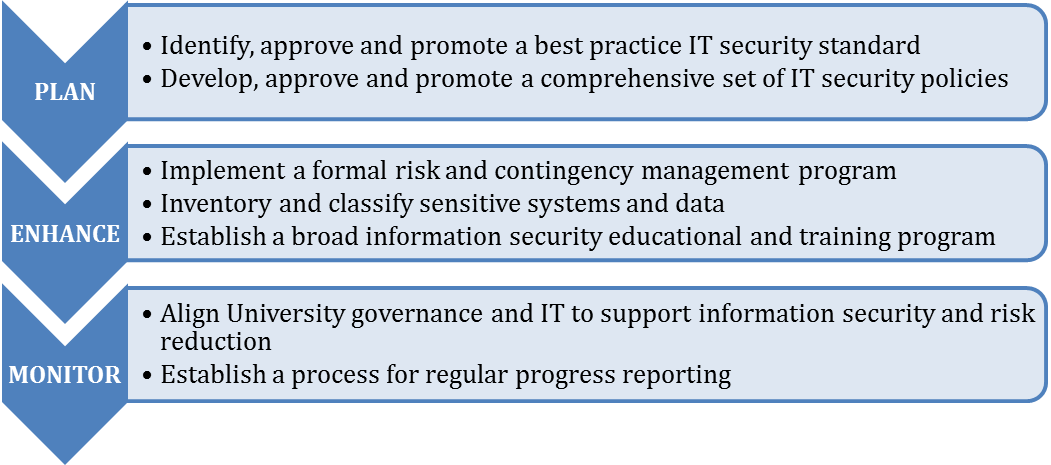
Figure 1 – Information Security Strategic Plan
 Plan
Plan
The plan phase aims at setting an industry accepted standard-based information security baseline and minimum requirements for implementing ETSU’s information security program.
-
Goal 1: Identify, approve and promote a best practice IT security standard. Percentage Complete 100%
- Select and promote an IT security Standard.
- Seek approval from university stakeholders.
Stakeholders: CISO, HCO and IT Internal Auditor, IT Security Subcommittee, IT Governance.
Estimated completion time: 3-6 months.
Goal dependencies: None. -
Goal 2: Develop, approve and promote a comprehensive set of IT security policies. Percentage Complete 50%
- Develop policies based on the approved IT security standard.
- Seek feedback and approval from university stakeholders.
- Publish policies for public comment when appropriate.
- Seek approval from the board of regents when appropriate.
- Post policies on university website.
- Implement technical and management controls based on the approved policies.
Stakeholders: CISO, HCO, ITS staff, IT Internal Auditor, IT Security Subcommittee, IT Governance.
Estimated completion time: 3-5 years.
Goal dependencies: Goal 1.
 Enhance
Enhance
The enhance phase identifies potential risks in critical business functions and provides actionable plans to reduce the risk to an acceptable level. In this phase, the university is focusing on attack prediction, exposure prevention, breach detection and incident response through continuous monitoring and data analytics.
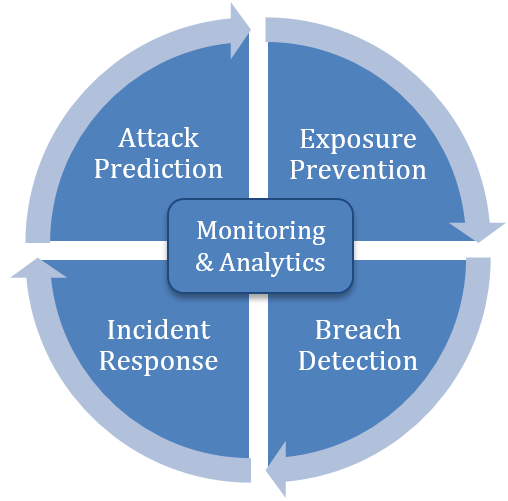
Figure 2 – Measurable continuous cyber improvement process
-
Goal 3: Implement a formal risk and contingency management program. Percentage Complete 50%
- Select a BIA model that best fits the university timeline and resources.
- Identify critical business units for a BIA.
- Develop a BIA for the selected business units.
Stakeholders: CISO, CIO, ITS staff, business critical units.
Estimated completion time: 2-3 years.
Goal dependencies: None. - Conduct a risk assessment for the mission essential functions and processes, critical
systems, and sensitive information identified in the BIA
Stakeholders: CISO, CIO, ITS staff, business critical units.
Estimated completion time: 1-2 years.
Goal dependencies: BIA completed. - Develop a DRP for the university data center(s) and core network infrastructure.
Stakeholders: CISO, CIO, ITS staff, business critical units.
Estimated completion time: 1-2 years.
Goal dependencies: None. - Develop a Continuity of Operation Plan (COOP) with the business-critical units.
Stakeholders: CISO, CIO, ITS staff, business critical units.
Estimated completion time: 1-2 years.
Goal dependencies: None.
-
Goal 4: Inventory and classify sensitive systems and data. Percentage Complete 15%
- Select a system and data discovery model that best fits the university timeline and resources.
- Discover and inventory sensitive systems and data.
- Work with data owners to provide a data classification matrix for the discovered data.
- Distribute the data classification matrix to each stakeholder and revise relevant policies.
Stakeholders: CISO, CIO, HCO, data owners.
Estimated completion time: 3-5 years.
Goal dependencies: None. -
Goal 5: Establish a broad information security educational and training program. Percentage Complete 25%
- Research in-house vs. commercial information security awareness training options.
- Map training solution with requirements from the security awareness training policy.
- Select and implement an information security awareness training program.
- Use metrics to continuously improve the training program and material.
Stakeholders: CISO, HCO, IT Internal Auditor, ITS staff.
Estimated completion time: 2-3 years.
Goal dependencies: Goal 2, information security awareness training policy.
 Monitor
Monitor
The monitor phase provides metrics to identify gaps in the information security program. The program is assessed for continued alignment with university goals and to ensure it is operating within the university’s risk appetite. Security vs. usability is also assessed in this phase to provide an adequate balance between risk reduction and ease of doing business.
-
Goal 6: Align University governance and IT to support information security and risk reduction. Percentage Complete 75%
- Monitor the makeup, effectiveness, and outcomes of current IT security governance.
- Research and re-align IT security governance structure and efforts as needed.
- Monitor information security efforts and outcomes with tools and metrics.
- Determine the need for additional information security support.
Stakeholders: CISO, CIO.
Estimated completion time: 3-5 years.
Goal dependencies: None. -
Goal 7: Establish a process for regular progress reporting. Percentage Complete 100%
- Build a website to aggregate security information and efforts.
- Post the IT Security Strategic and Tactical plans on the web.
- Post approved university information security policies.
- Provide updates on the progress of this plan.
Stakeholders: CISO.
Estimated completion time: 6-9 months.
Goal dependencies: None.
icons from font awesome http://fontawesome.io/
 David Collins Way Road Closur...
David Collins Way Road Closur...